Open Doors
I didn’t know I was so bad off and I certainly didn’t know I have so many money making opportunities!
In the past few weeks, I’ve been notified that:
- If I don’t pay my taxes, I’m heading for jail.
- My system needs to be updated but a simple click will make the problems go away.
- I will soon face foreclosure on my home.
- I need to update some of my paid-for phone apps by visiting several sites.
- My car warranty is about to run out.
- A couple in England won the lottery and want me to have $1M.
- A guy with a name similar to mine named me as his sole beneficiary.
- A woman dying of thyroid cancer found religion and wants me to distribute her fortune to humanitarian causes.
- I have unspeakable things in my gut but…there’s a simple way to get rid of ‘em.
- A number of stores and banks have asked me to verify orders and withdrawals.
Yeah, it’s some folks in Florida (the largest concentration of spam, etc in the U.S.) and other countries phishing for your information.
Phishing is actually like fishing – drop a line into the Internet and reel in the suckers – only more techie.
Some of the requests are remarkably “real” looking but the goal is always the same: get you to go to a website that is infected with malware–hostile or intrusive software, including computer viruses, worms, Trojan horses, ransomware, spyware, adware, scareware and other malicious programs.
They don’t want much though.
Just your username, passwords, credit card info and anything they can scrape from your device/system to make a buck.
But you won’t fall for those stupid emails because you’re dumb, not stupid!
Instead, you’ll stick with your social media options to talk with people – Facebook, LinkedIn, SmartChat, Twitter, Google + and Pinterest.

Surprise!
Right. They know where you waste (ooppss invest) your time with your devices.
They’ve gotten increasingly smart in their acquisition of knowledge through social engineering techniques.
They get real personal with spear-phishing (very one person directed) attacks through social media to learn the name of your boss or significant other(s) just by scraping it off LinkedIn.
They even create a clone of a website and tell you to enter personal information, which is then emailed to them.
The site looks real and you’ve been there dozens of times before so you click on it and BAM! you’re owned.
Cyber criminals have figured out that they can make money more easily than with drug deals and there’s a lot less risk in being caught.
For them, the nice thing about social media is that there are so many fish in such a small barrel.
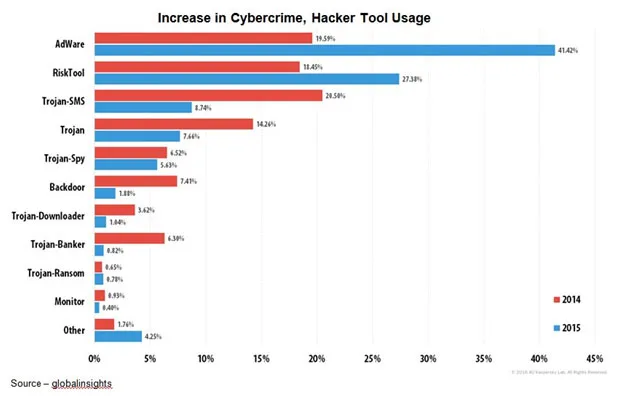
In the 40 years malware has been around, the industry has found ways to defeat a growing range of malware types. Unfortunately, the bad guys are always one step ahead and are often out of reach in some location where they can’t be touched.
According to a number of cybersecurity specialists, the ugly truth is, “If you haven’t been hacked yet, it’s because you don’t know you’ve been hacked.”
With folks living, doing almost everything on their smartphones, life is even better for the crooks because so many people download all the free apps that are available … even though they’re only semi-done.
While Apple rigorously tests apps before they are made available, the other two guys (MS and Google) do a so-so job of testing and verifying the quality of the app so there are tons of entry points.
The phone is such a great always with you, always on work/play/entertain/communications tool that few people think a lot about security for it. So hackers have been first in line to deliver great mobile sites. In other words, you’re playing security roulette!
Strengthening security on all of your devices is cheap and simple.
Keep your OSes current with all of the patches.
Add antivirus and malware software – not just the free stuff, pay a few bucks and get the full package–and keep them updated.
Add computer, tablet and smartphone firewalls.
Oh yes, and face a brutal fact … your passwords probably suck!!!
Don’t think so?
According to a recent Web study, here are the 20 most popular passwords (the ones hackers try first):
– 123456 – 12345 – 123456789 – password
– ilove you – princess – rockyou – 1234567
– 12345678 – abc123 – Nicole – Daniel
– babygirl – monkey – Jessica – lovely
– Michael – Ashley – 654321 – qwerty
If yours isn’t on the top 20 list, don’t look so smug.
The bad guys have systems that can fire thousands of password guesses a minute at your device.
They also:
- Use brute force based on your public info like family names, birthdays, info you spread around the web
- Generate guess answers to password-reset questions like 25 random things about you – mother’s maiden name, place of birth, color of first car, wife’s/kids’ names
- Create a word list based on your profile web pages and postings
Gawd, you just make the thief’s job too easy!
Don’t give us the line that all of your devices are from Apple and their stuff just doesn’t get hacked. The next thing you’ll tell us is that their stuff doesn’t crash!
Security folks recommend passwords that are 20 characters or longer and contain a mix of characters.
The longer the password, the harder it is to crack.
Okay, so you can’t remember 20 different passwords that are that long. You do use a different one for all of the important places you go, right?
That’s why people developed (and sell) password managers, which use software to encrypt passwords. Password managers store all of your logins and passwords, usually encrypted, so you can paste them into the form (some will load automatically for you).
Too much trouble? Well think about the ugly fact that your device is a partially unlocked door to your family jewels … and probably your boss’.
But wait, there’s more!
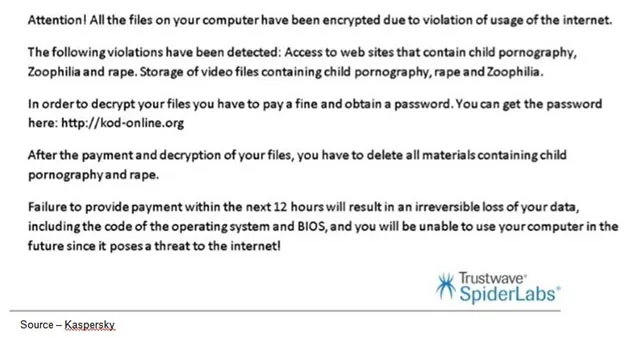
There’s a new game in town that hackers have started playing called ransomware.
McAfee reported a huge jump from 257,357 new ransomware samples in the first half of 2014, to 380,652 in the second half. By the first half of 2015, that number jumped 5.3 times to over 2 million.
The company said the growth is likely to continue, in part because of the offer of “Ransomware-as-a-service.”
These guys/gals are raking in hundreds of millions of dollars extorted from companies large and small and individuals like you.
And catching them is almost freakin’ impossible.
The latest version of ransomware security out there is so good even cyber experts can’t hack (reverse hack?) it.
It comes into your device like regular malware through untrusted sites, clicking on nasty attachments, etc.
That’s where the similarity ends because now, they outright give you a ransom note – send us $500 or a whole lot more – and we’ll “set you free.”
To minimize the opportunity of having them attack your device, one security expert recommended getting rid of potential malware gateways like Flash and Silverlight.
Another suggested installing an ad blocker and NoScript browser add-ons since ads have become a very popular vector for the spread of malicious malware
Anyone can fall prey to these kinds of attacks; yes, even me.
We got hit with a very early version and:
- It scared the hell out of us
- I knew I hadn’t visited any of “those” sites and didn’t have any of “that” stuff on my device(s).
- After figuring out it wasn’t really me, it made me mad as Hell.
- It took four hours, two IT experts and one six-pack to get rid of it
Now?
- Make certain everything is current every day.
- Run my malware and anti-virus apps every evening.
- If I have my doubts about a site, I don’t go there.
- I hardly open anything (previewing first).
- I do two complete backups to external (offline) drives monthly.
- I pass stuff through the cloud but don’t store anything I really want there.
- And I hope to gawd I never have to strip and restore everything.
It may be overkill, but malware and ransomeware is becoming more prolific and I’m only one guy with six different devices against some of the smartest (sneakiest) folks around.
 I know I should feel sorry for the poor, hungry hackers, cybercriminals, script kiddies; but I can’t.
I know I should feel sorry for the poor, hungry hackers, cybercriminals, script kiddies; but I can’t.
However, I’m not as sour about humanity as Mike was when he said, “What I’m talking about comes down to a more basic philosophical principle: Don’t trust nobody.”
I still trust my wife, my kids and you – sorta’, kinda’.
# # #